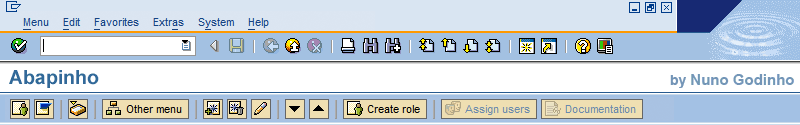
Request Based Debugging

If you look up the UNAME system variable in debug within a RFC call you may think it kind of odd to find a username that is not your own. What happens is that the system adopts a specific username for remote calls and a new session is started. A new session implies a new execution context and, hence, all our strategically placed breakpoints will no longer be recognised.
This problem can hinder a simple debug forcing us to run through the code looking for THAT remote call to THAT particular system.
SAP has a solution.